Enterprise Threat Hunting

Introduction
Hunting for attackers in your logs
Hunting for attackers in the network traffic
Hunting for attackers on the endpoints
Hunting for attackers in your cloud environment
Productivity Hacks to Get More Done in 2018
— 28 February 2017
- Facebook News Feed Eradicator (free chrome extension) Stay focused by removing your Facebook newsfeed and replacing it with an inspirational quote. Disable the tool anytime you want to see what friends are up to!
- Hide My Inbox (free chrome extension for Gmail) Stay focused by hiding your inbox. Click "show your inbox" at a scheduled time and batch processs everything one go.
- Habitica (free mobile + web app) Gamify your to do list. Treat your life like a game and earn gold goins for getting stuff done!
Be the first to add a review.
Please, login to leave a review

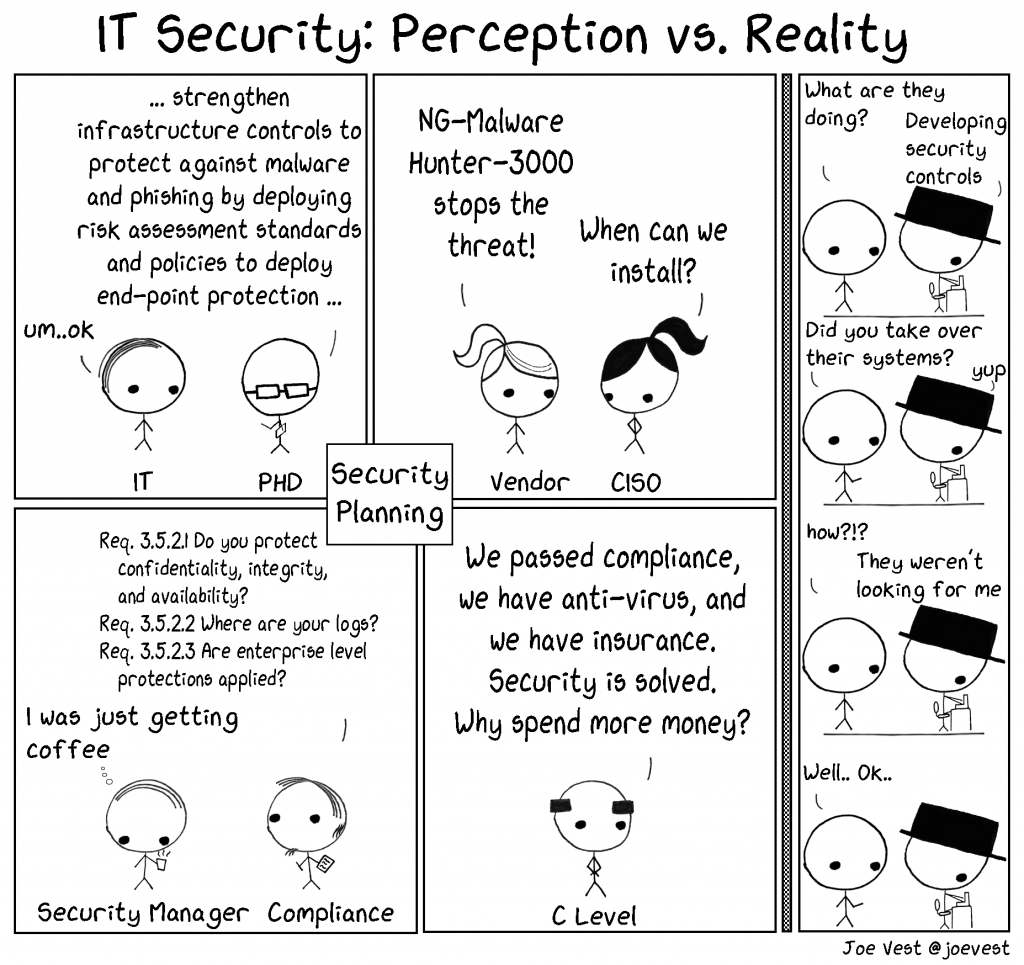 Are you looking for “them”?
Are you looking for “them”?

